As wealth has moved from physical to digital assets, the risk of cybercrime has become an increasingly prevalent issue for businesses. Globally in 2020, the average cost of a data breach was $3.86 million and cybercrime damages are predicted to cost up to $10.5 trillion annually by 2025. As hackers get more sophisticated, they are no longer just going after easy targets for a quick pay out and are targeting larger organisations with complex operations, such as those in the cold storage industry, for greater ransoms. With cold storage logistics providers being connected at multiple points across the supply chain, there is a high risk of disruption if a cyber-attack was to occur.
What is a cyber-attack?
A cyber attack can be defined as an unwelcome attempt to steal, expose, alter, disable, or destroy information through unauthorised access to computer systems (IBM).
Key types of cyber security threats
Hackers are always looking for new methods to exploit weaknesses in security protocols, with common cyber threats including:
Phishing:
Phishing is one of the most common cyber security threats, with over 3/4 of cyber breaches or attacks on businesses being phishing attacks. Phishing attacks are when hackers send a fraudulent message (often emails) designed to get people to reveal sensitive information to the attacker, enabling them to deploy malicious software on the victim’s infrastructure, such as ransomware.
Ransomware:
Ransomware is a type of malware that is designed to deny a user’s access to files, data or systems, with the threat of erasing or publicly leaking the data, unless a ransom is paid to the attacker.
Malware:
Malware encompasses a variety of malicious software attacks that provide unauthorised access or cause damage to a computer. They are often installed on the victim’s system when a user clicks a dangerous link or email attachment.
DDoS Attacks:
A Distributed Denial-of-Service (DDoS) attack is when servers or networks are overloaded with traffic in an attempt to crash it, so it is unable to respond to any legitimate requests. A DDoS attack is launched with the goal of taking a system offline, often so another attack can be launched onto the network.
Why are Cold-Storage businesses liable for cyber-attacks?
Being connected at so many points of the supply chain makes organisations in the cold storage industry vulnerable to cyber-attacks. Due to the high cost of systems outage and temperature-controlled aspects of cold storage logistics, any disruptions due to a cyber attack can be extremely costly. Time and temperature are essential to maintain for cold storage to avoid spoilage and loss of revenue.
Organisations using older, legacy software solutions to run their operations are often more liable to cyber-attacks, as the latest security protocols aren’t included within the software, making them more vulnerable.
So how can you prevent cyber-attacks?
Unfortunately, is no way of completely avoiding a cyber-attack to your business, but there are measures you can put in place to stay one step ahead to prepare and protect your business from any potential damage.
How can Microsoft technology help you avoid a cyber-attack?
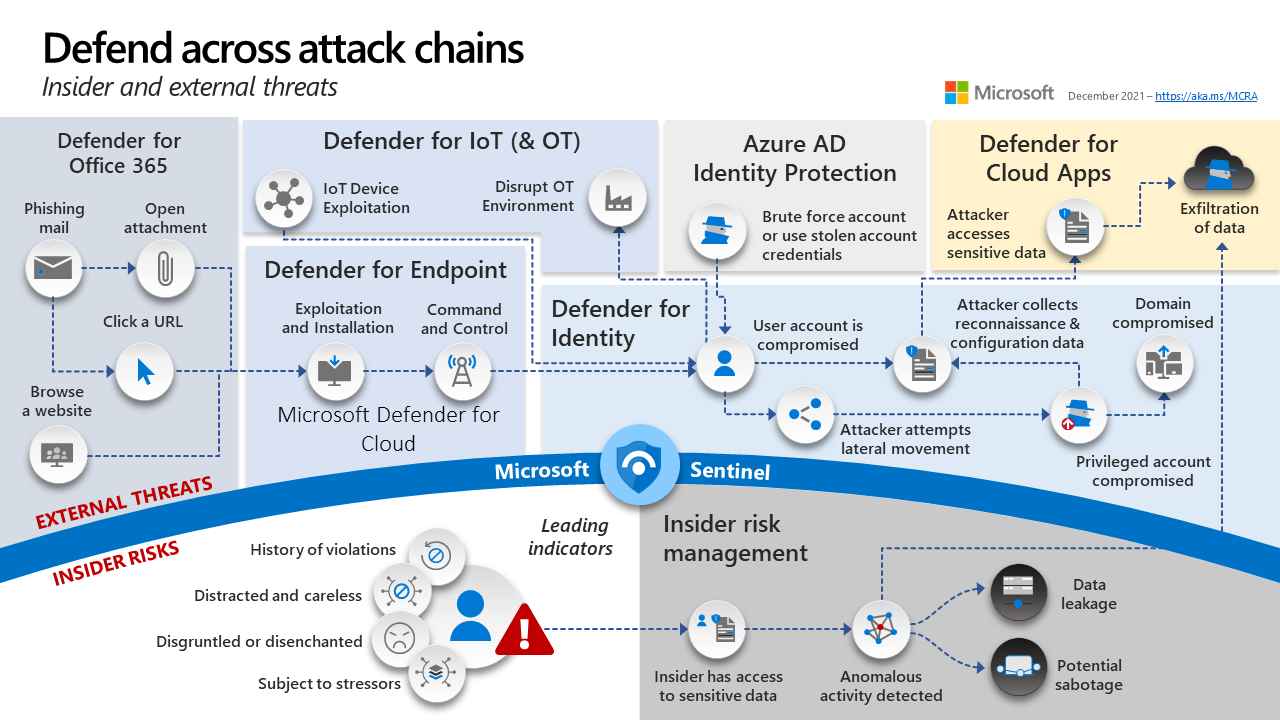
Microsoft are constantly striving to help businesses in any industry across the world stay one step ahead of hackers, with continual investment into their cyber security protocols.
Start with a secure foundation – Microsoft’s huge investments into cyber security infrastructure for both cloud and physical data centers helps give you peace of mind from the threat of cyber-attacks.
Simplify security with built in controls – Easy-to-use controls and services mean you don’t need to worry about what is happening with your data, no matter whether it is emails, spreadsheets or ERP/CRM data, you are always protected.
Detect threats early with unique intelligence – Microsoft have implemented protocols that are informed by real-time global cybersecurity intelligence. Using machine learning, behavioural analytics and application-based intelligence, these insights help you detect threats faster and minimise risk for your organisation.
Microsoft’s threat intelligence is utilising powerful machine learning and AI systems to enable them to monitor 24 trillion signals daily, including 1.2+ billion PCs, servers and IoT devices.
As seen in the image below, both external and internal threats are being monitored through the technologies Microsoft have implemented to make sure your data is safe.
7 Practical Cyber Security Tips from Microsoft
So, what steps can you take now to improve the security of your organisation?
- Require antivirus and security software
- Manage identities and access
- Protect Devices
- Lock unattended machines
- Consider a VPN for Remote Access
- Provide security training and reminders
- Use secure tools built for business
While the first 6 tips are simple, practical ways of improving the security, it should be noted that point 7 is paramount, especially for those in the cold chain. Modern, intelligent systems give you the highest level of safety available and lower the risk of any cyber breach.
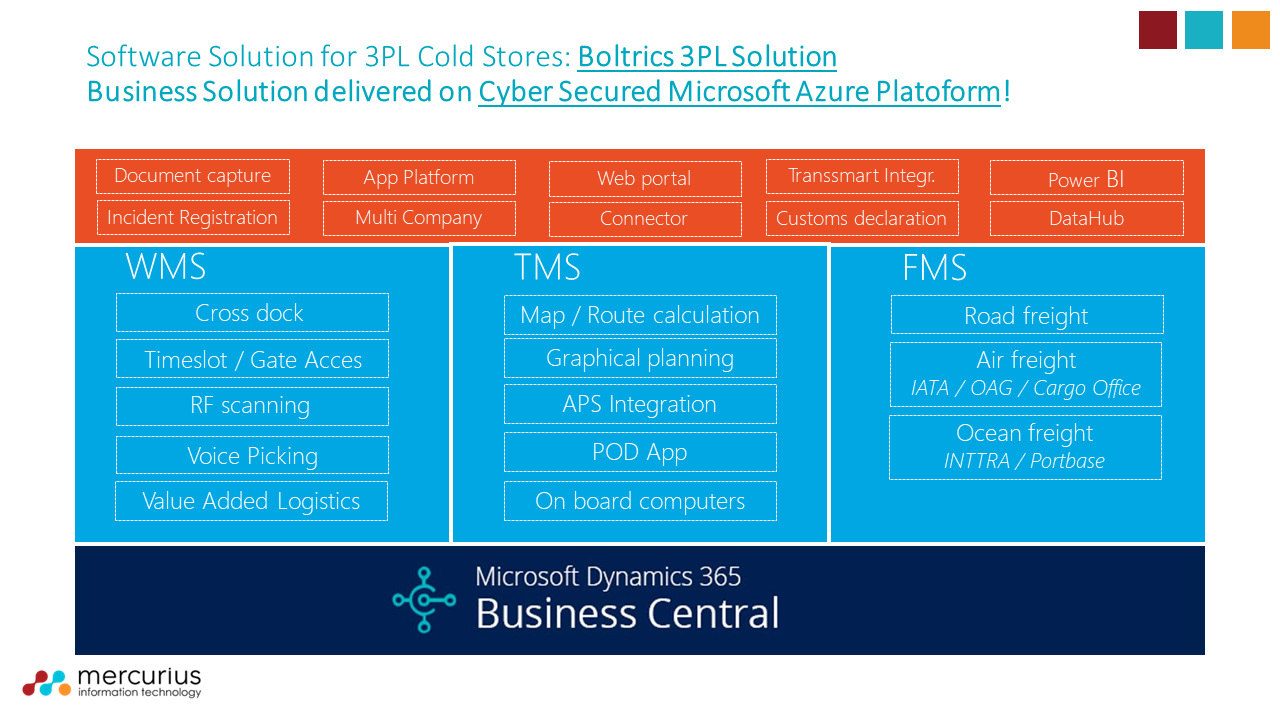
Secure your cold-storage business with Boltrics 3PL Dynamics
For those in the cold storage logistics industry, we recommend using Boltrics 3PL Dynamics solution to run your operations securely. Developed on the Microsoft Azure platform, this modular WMS, TMS, and FMS solution incorporates all your primary business processes into a single software solution, to help future-proof your business. 3PL Dynamics is also built directly on Microsoft Dynamics 365 Business Central ERP, helping cover back-end processes such as financials, sales, customer service, HR and more. Instead of endless deployments with high risks, what you get is a complete and quickly deployable system which connects seamlessly with the processes and roles within your organisation.
Would you like to learn more about cyber security for the cold-storage industry?
Founder and Managing Director or Mercurius IT, Jay Tahasildar, recently spoke at an event for the Cold Chain Federation on the rising threat of cyber crime to the cold chain.
Click below to view the full event recording on-demand.
Alternatively, if you are looking to improve your organisation’s cyber security, we are offering a ‘Cyber Security Readiness’ audit to assess your current protocols and vulnerabilities and see how they can be improved.
Leave your details in the contact form to get started.